My role
Led the research, creation of the north star vision, creation of the new RBAC model, and UX of the new experience. Oversaw the visual design.
Team
Cross functional collaboration between design (3 designers including myself), research, architecture/engineering, and product management.
Timeline
6 months
Discovery & research
I led the initial discovery and research phase by consulting with architects, engineers, and technical sellers to understand the as-is access control experience and known pain points. I then co-designed a generative study with the UX Research team, personally conducting 7 interviews with external users. This research uncovered that:
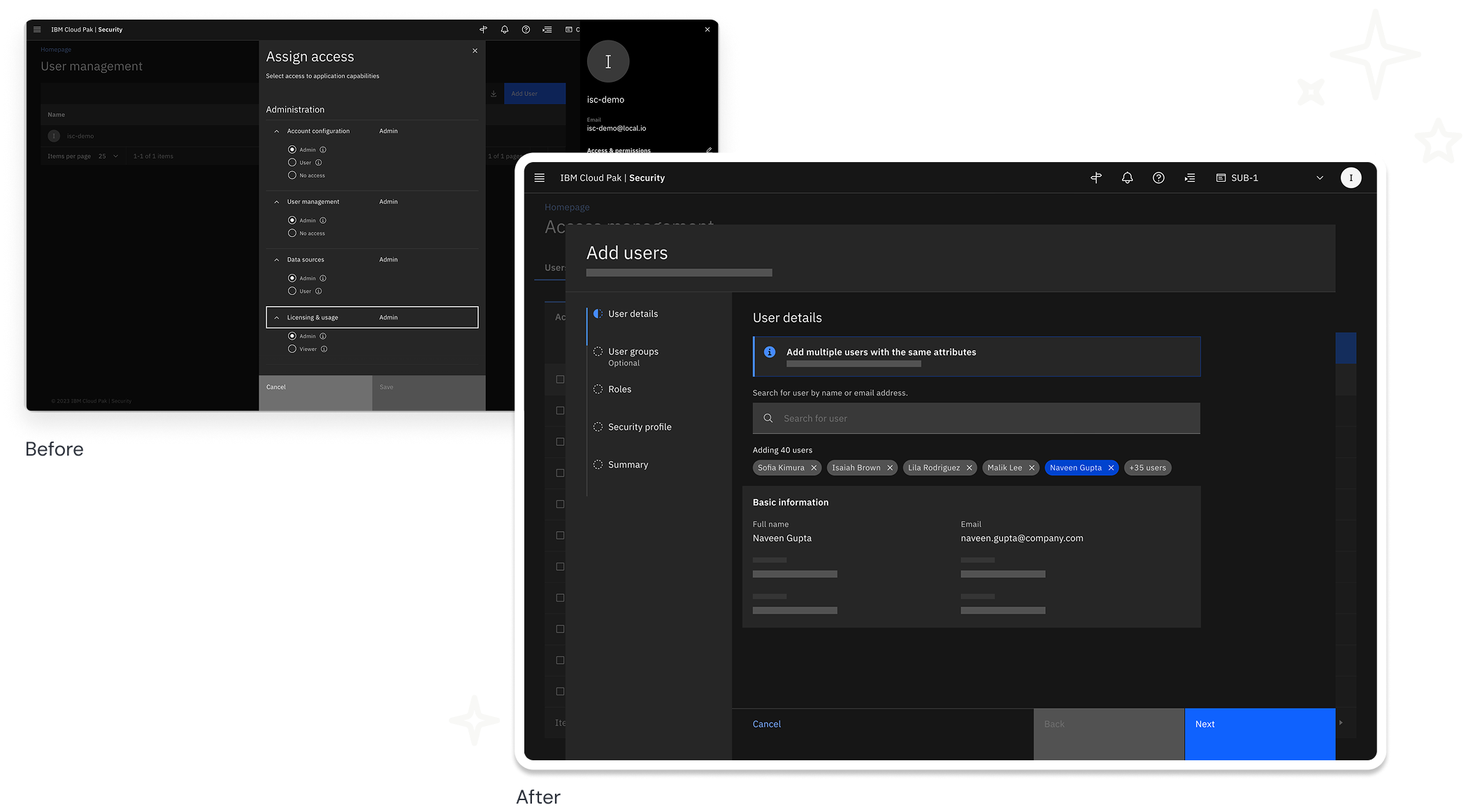
The existing experience was difficult to use and lacked basic features users expected.
Varying security team sizes and structures required a highly flexible, access model.
Customers trust a granular access control model supporting the principle of least privilege.
“Right now, [some features are] pretty much unusable in a production environment that has more than like 5 people.”
— IBM technical seller


Strategy
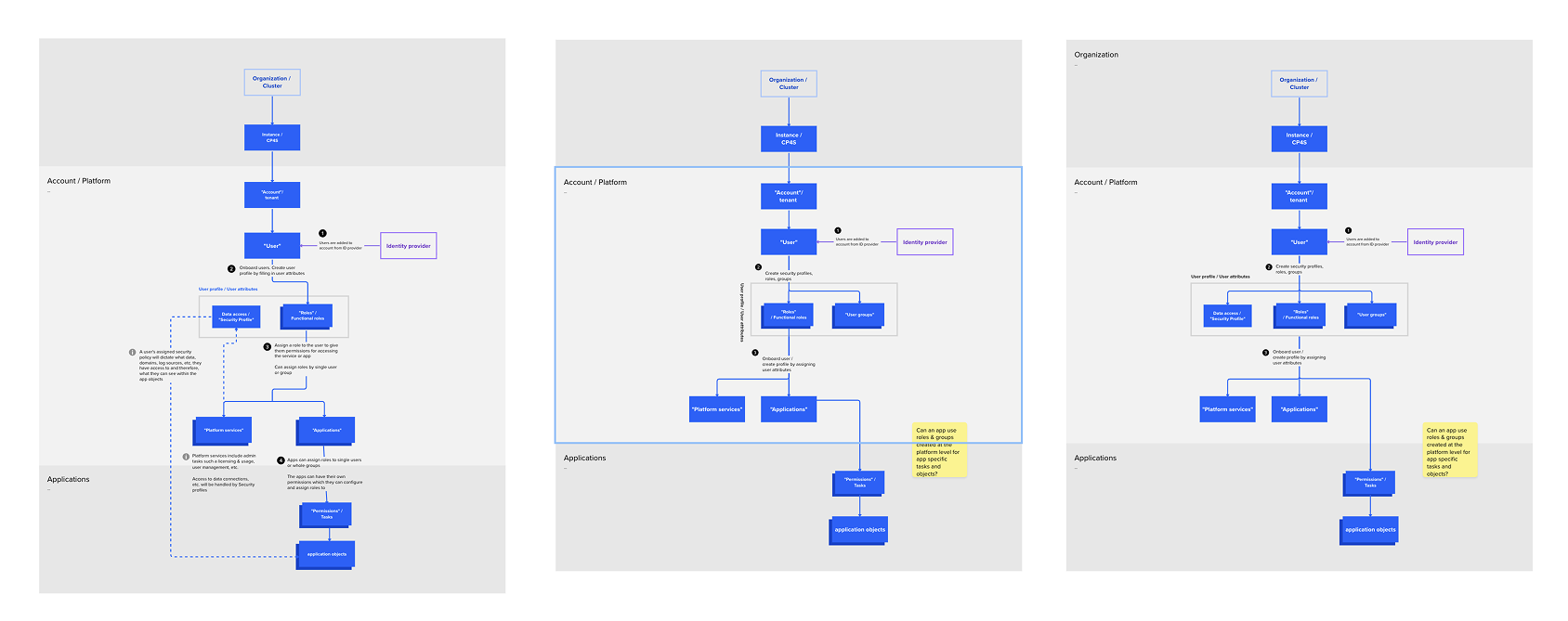
I facilitated remote, cross-functional workshops to align the product team on a unified vision, prioritizing the flexibility and usability requirements identified in our user research as foundational to security. Our core strategy:
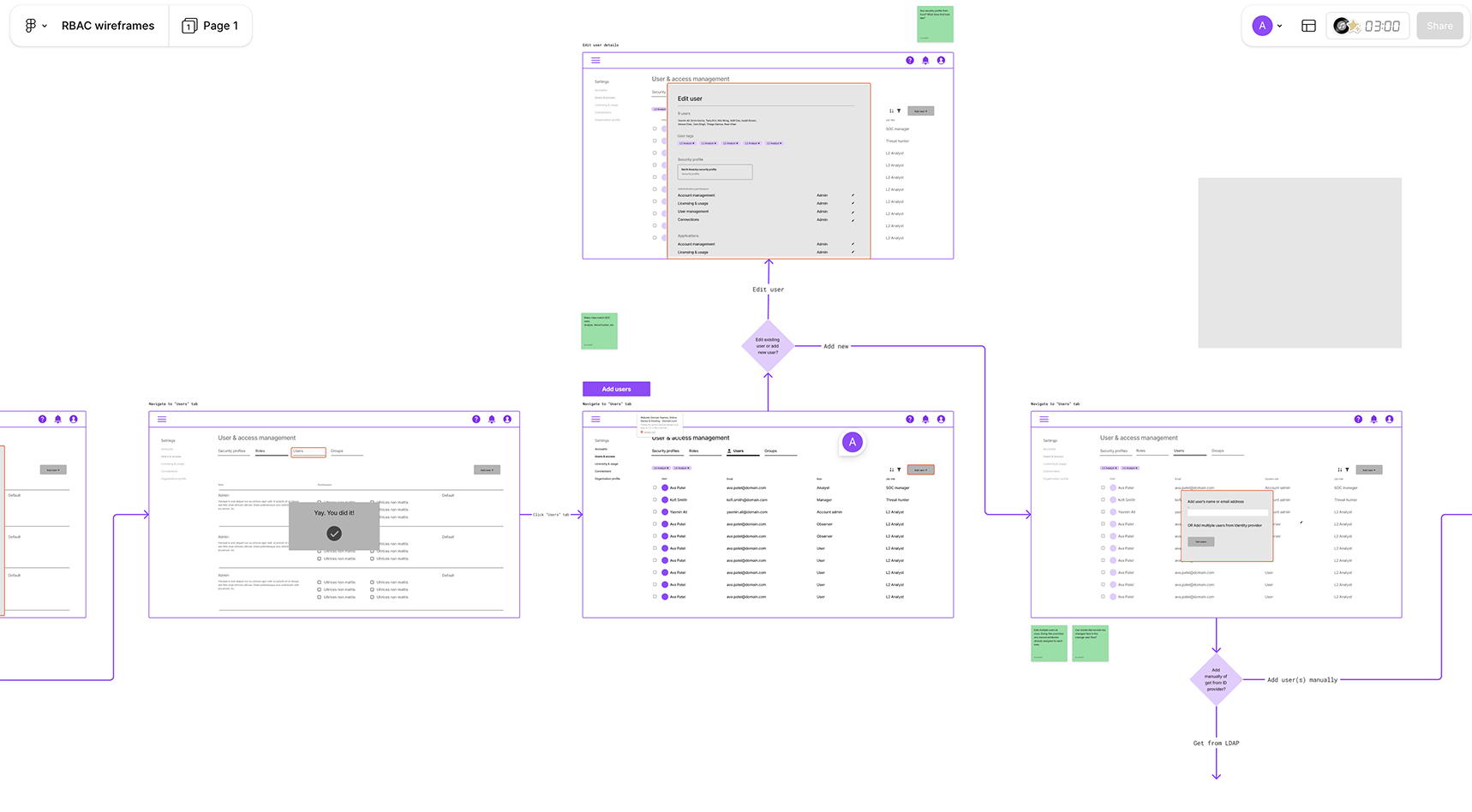
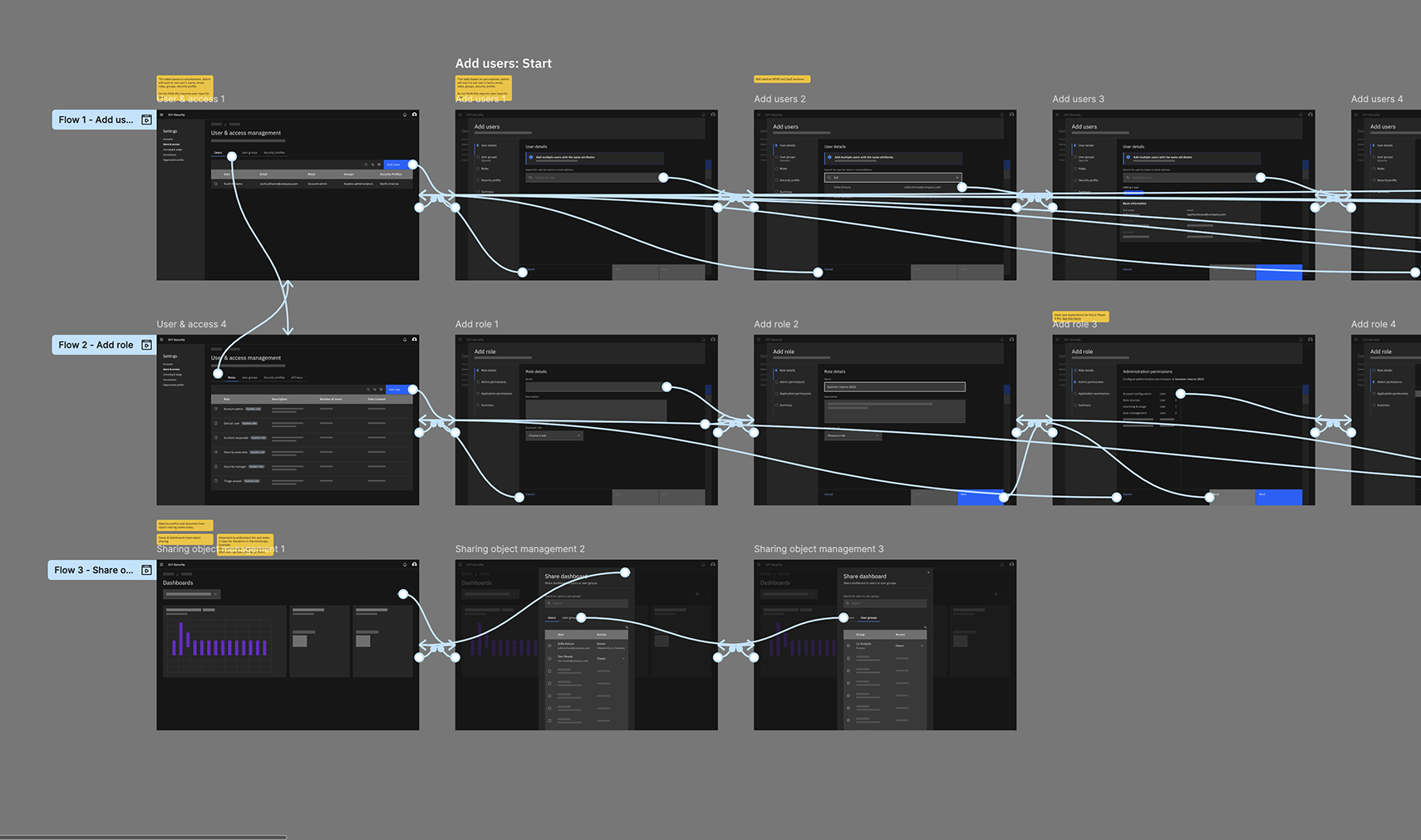
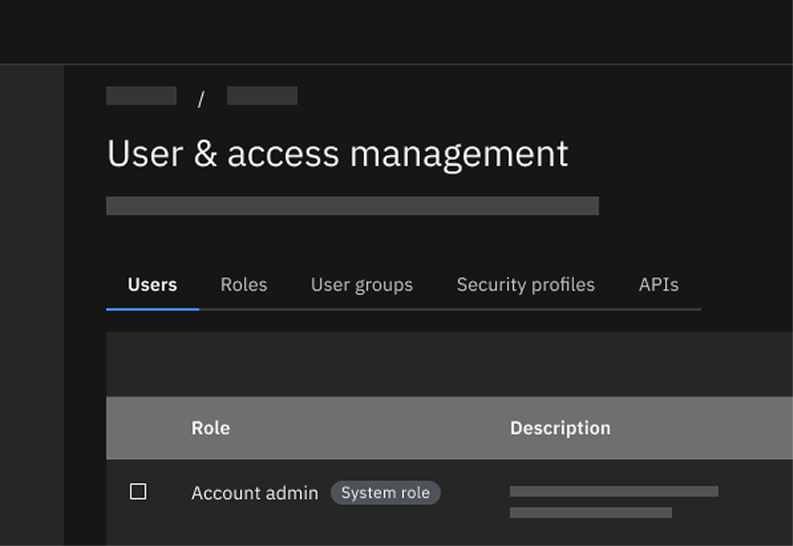
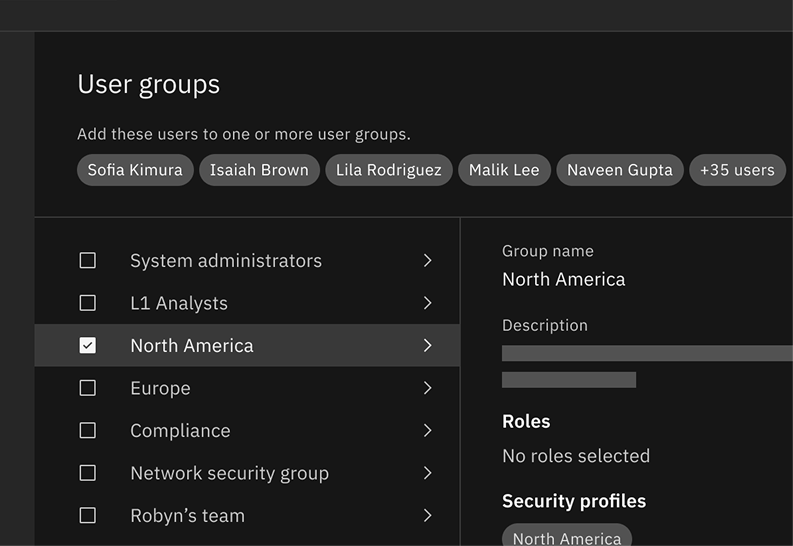
Centralize the access control experience within the UI that allows admins to easily govern user and data access in a single location.
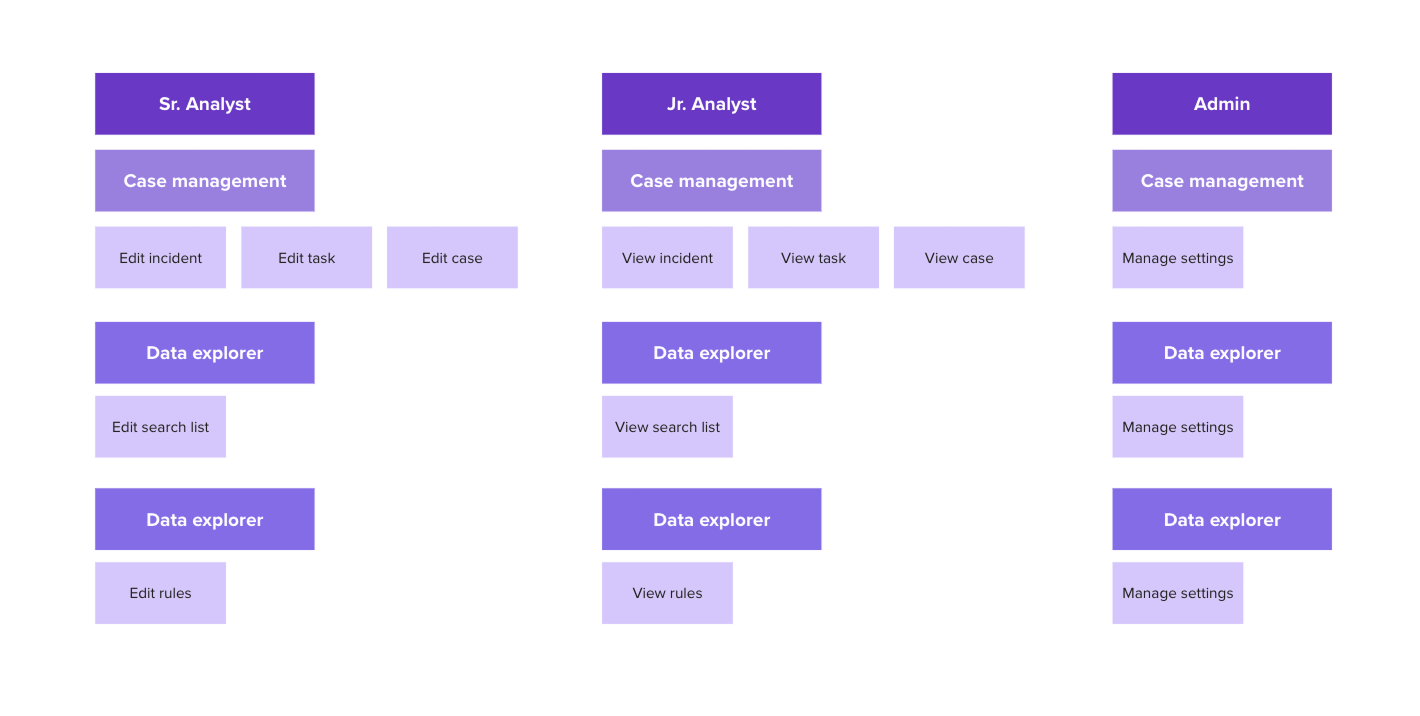
Introduce roles and groups so admins may organize their end users in a way that matches their mental model, increasing efficiency and reducing errors.
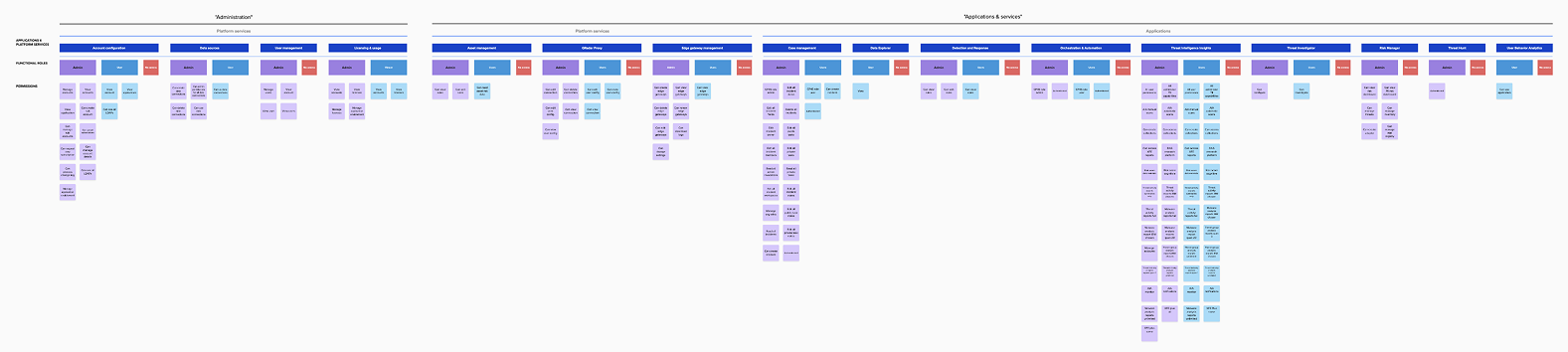
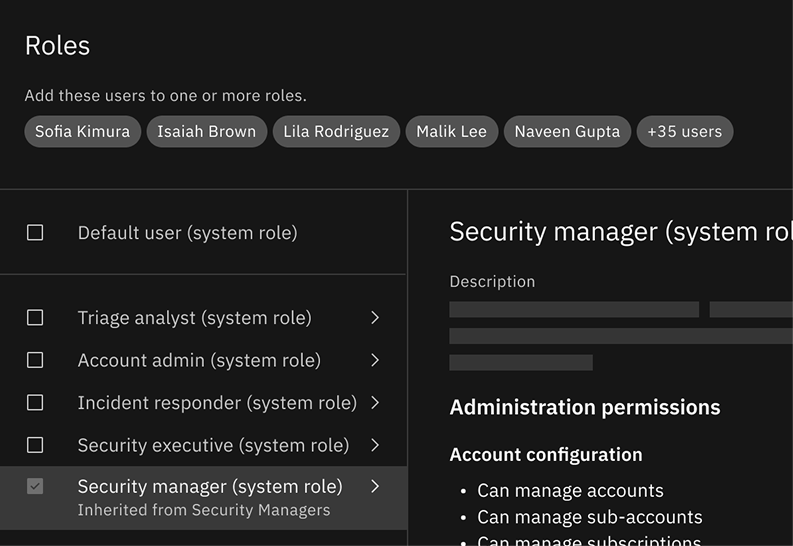
Restructure permissions to give admin more granular control when granting access and allow room to scale as new permissions are added.
Results
The redesign delivered a centralized hub for managing users, roles, groups, and permissions. Easy workflows and clear explainability reduce the time and effort it takes to . Most significantly, the new permission model removed critical technical blockers that were stalling platform modernization and customer adoption.
Granular permissions and categories that match the users’ mental model
Introduce roles and groups so admin may organize their end users in a way that matches their mental model, increasing efficiency and reducing errors.
Flexibility to accommodate future growth
Visual design by Eric Lam.


